AI vs SOC: Defending Against Machine-Speed Attacks
1. Overview AI-driven attacks now operate at machine speed, exposing gaps in traditional SOC capabilities. Defending against them requires faster decision-making, adaptive controls, and Artificial Intelligence-augmented security strategies. 2. The New Threat Reality of AI Attackers use Artificial Intelligence to automate reconnaissance, phishing, and exploitation in seconds—bypassing static defenses and reducing response windows. 3. Evolving […]
Autonomous Red Team Agents: The Future of Continuous Attack Simulation
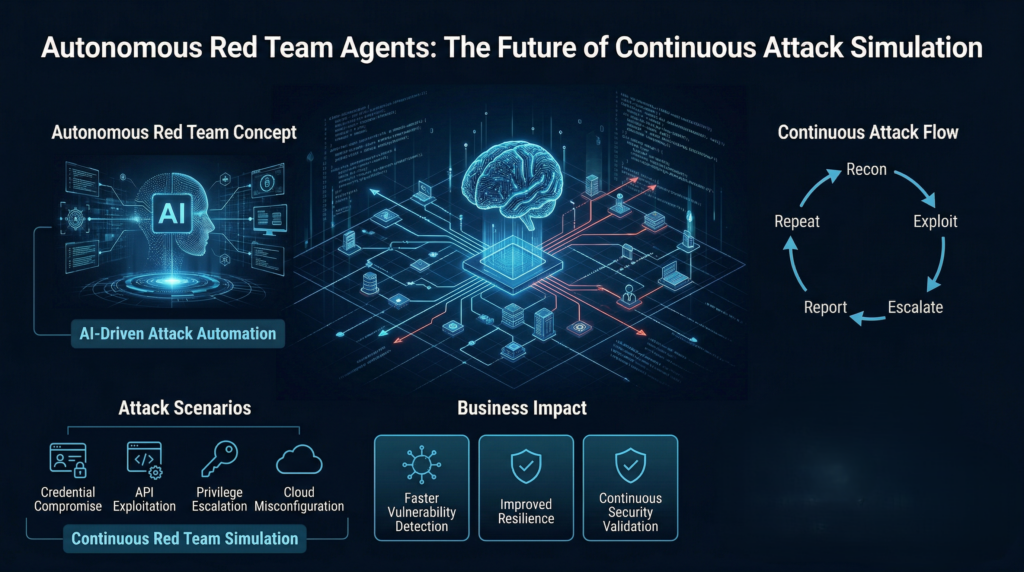
1. Introduction Autonomous Red Team agents are redefining how organizations test and strengthen their security posture. Furthermore, continuous attack simulation powered by AI enables faster identification of vulnerabilities across complex digital environments. Specifically, modern threat actors leverage automation and intelligence which demands equally adaptive defensive strategies. On a positive side, organizations adopting such automation gain […]
Using AI to Bypass Fraud Detection Systems: A Red Team Perspective

1. Overview AI has transformed fraud detection-but attackers are leveraging the same capabilities to bypass it. Specifically, Red Team exercises reveal how intelligent automation can quietly exploit even advanced security systems. 2. How AI Enables Evasion Modern adversaries use AI to: Above all, these techniques allow malicious activity to blend seamlessly into legitimate operations. 3. […]
Weaponizing Generative AI for Phishing Campaign Simulation in Banking Environments
01. Introduction Generative AI is rapidly transforming cybersecurity practices across financial institutions. Thus, advanced threat actors now leverage Generative AI to craft highly convincing phishing attacks, making traditional defenses less effective. Furthermore, controlled simulation of such attacks enables banks to strengthen detection, response and employee awareness against evolving threats. 02. Rising Sophistication of AI-Driven Phishing […]
SOC 2026: Next-Generation Security Operations for Global Banks

Executive Imperative By 2026, traditional Security Operations Centers (SOC) will be obsolete. Global banks operate in cloud-first, high-volume, fraud-intensive environments where attacks are faster, more targeted, and AI-enabled. As a result, Incremental upgrades are insufficient. Thus, SOC transformation is now a strategic necessity The Core Requirements 1. Intelligence-Led Detection SOC architectures must integrate both global […]
AI-Powered Phishing & Credential Harvesting: The Escalating Cyber Threat Reality

1.0 Executive Snapshot Artificial Intelligence has industrialized cybercrime. Accordingly, phishing campaigns are now automated, additionally, hyper-personalized and nearly indistinguishable from legitimate communication. Moreover, attackers exploit human trust at scale, resulting in accelerated breach timelines and thereby amplified financial impact Thus, the threat is no longer emerging – it is operational. 2.0 How the Threat Has […]
Corporate Governance & Rise of Cyber Accountability

As digital transformation accelerates, cybersecurity has become a core governance issue. Specifically, data breaches, privacy failures, and unethical technology use now pose direct risks to business continuity, reputation, and trust. Furthermore, addressing them requires leadership accountability—not just technical controls. Why Cyber Accountability Matters Cyber risk is no longer confined to IT. Rather, it is a […]
Top Cybersecurity Priorities for 2025: CISO Insights

Cybersecurity is no longer just an IT concern—it is a core business and leadership issue. As threats grow faster and more sophisticated, a single incident can disrupt operations, damage trust, and directly impact revenue. In 2025, organizations must focus on the security priorities that truly reduce risk and strengthen resilience. Why Priorities Matter Attackers now […]
API and Open Banking Security: When Interconnectivity Becomes a Systemic Financial Risk

1.0 Introduction API-driven platforms now form the digital backbone of the global financial system. Payment processing, account aggregation, embedded finance, digital lending, and open-banking ecosystems all depend on continuous data exchange between banks,fintechs, and third-party providers. This architecture has accelerated innovation-but it has also expanded attack surfaces at a speed most institutions are struggling to […]
Real-Time Fraud, Deepfakes, and Synthetic Identities: The New Trust Crisis in Digital Banking

1.0 Introduction Digital banking has entered a new risk phase. Real-time fraud powered by deepfakes and synthetic identities is no longer an edge case – it is rapidly becoming a core threat to trust, liquidity, and customer confidence. In a world of instant paymentsand frictionless onboarding, fraud now succeeds at the point of authorization, not […]